Introduction
MCP (Model Context Protocol) is the recently announced standardized way for AI models to communicate with the outside world, announced by Claude. Specifically, in the context of accessing data from the outside world.
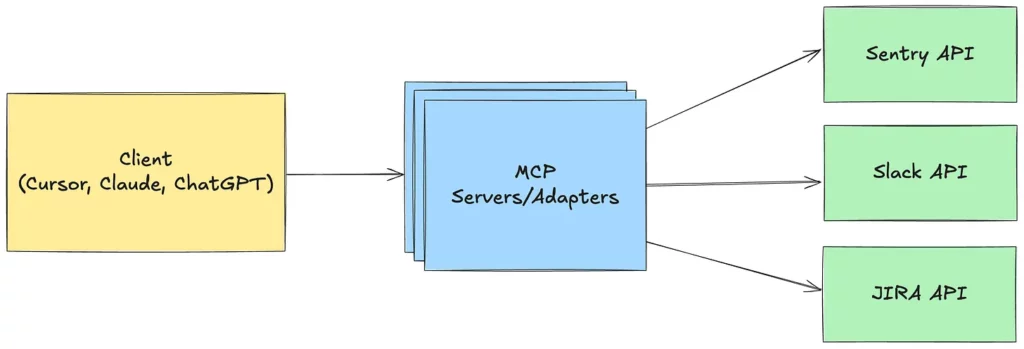
The above architecture shows that it’s an interface that is able to connect various kinds of APIs using a language that is familiar to AI models. It seems to be just a minor standardization, but it has triggered a creation of multiple new servers for more or less popular services. It’s easy enough that none of the big players want to be left behind, and everyone wants to provide an interface for contact between AI and their system.
You can see how popular it is when you look at the number of new implementations of this protocol.
https://github.com/punkpeye/awesome-mcp-servers
Let’s start by taking a closer look at what MCP (Model Context Protocol) is.
We have to start with the official MCP (Model Context Protocol) specification
https://modelcontextprotocol.io/specification
A short and simple explanation of what MCP is:
https://read.highgrowthengineer.com/p/mcps-simply-explained
Also, an interesting and more in-depth description of the protocol itself (MCP), as well as the possibilities for its use and potential future expansion:
https://a16z.com/a-deep-dive-into-mcp-and-the-future-of-ai-tooling
The big advantage of this new protocol, as well as its rapid adoption, is that it allows AI to use specialized tools to increase its efficiency. A good example of this is reverse engineering. So far, LLMs have had to rely on their own abilities to do this and analyze code purely at the language layer. With interfaces such as GhidraMCP (https://github.com/LaurieWired/GhidraMCP), it can take advantage of mature solutions and process already preprocessed data.
MCP and security
The topic of MCP security can be summarized up in one sentence:
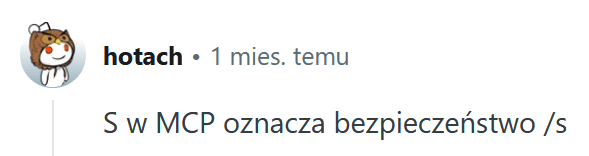
The article sums it up nicely:
https://elenacross7.medium.com/️-the-s-in-mcp-stands-for-security-91407b33ed6b
Tool Poisoning Attack threat description
https://invariantlabs.ai/blog/mcp-security-notification-tool-poisoning-attacks
You can also see the vulnerabilities that can exist in the MCP code by seeing the examples.
Intentionally Vulnerable MCP Server (Built to test SQL Injection (SQLi) and Remote Code Execution (RCE) vulnerabilities via FastAPI, JSON-RPC, and LLM-based decision logic.)
https://github.com/evrenyal/mcpsecurity
https://github.com/harishsg993010/damn-vulnerable-MCP-server
A very structured overview of MCP server threats with examples of problematic calls.
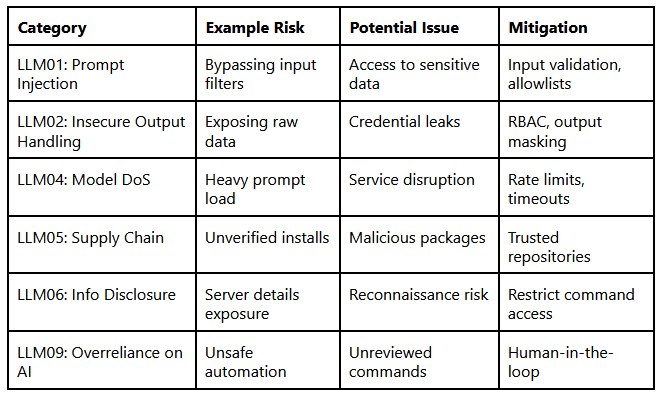
Another list of threats related to MCP servers:
- Command Injection Vulnerabilities – running malicious code passed in parameters.
- Tool Poisoning Attacks – injecting malicious instructions into the server’s action description.
- The Rug Pull: Silent Redefinition – the ability to substitute server behavior.
- Cross-Server Tool Shadowing – replacing the results of one MCP by another.
- Context Leakage Risks – a long-held session can leak sensitive information.
- Prompt Injection – overwriting the default behavior of a prompt by a response from an MCP.
- Memory Poisoning and Context Corruption – corruption of session context through a malicious response from MCP.
https://elenacross7.medium.com/️-the-s-in-mcp-stands-for-security-91407b33ed6b
https://invariantlabs.ai/blog/mcp-security-notification-tool-poisoning-attacks
https://medium.com/@sebuzdugan/understanding-the-security-implications-of-using-mcp-9bd3323ad42d
Here instead we have a very insightful analysis of MCP (Model Context Protocol) threats
- Name Collision – impersonation of trusted servers.
- Installer Spoofing – injection of an infected server.
- Code Injection/Backdoor – malicious code in a server implementation.
- Sandbox Escape – exiting a command outside a trusted environment and gaining unauthorized access to the operating system.
- Slash Command Overlap – conflict in the names of methods available to AI.
https://arxiv.org/pdf/2503.23278
So, how to defend against these threats?
There are many methods, but they can be summed up to a simple Zero Trust approach and taking care of classic security principles:
- session management,
- authentication and authorization,
- encryption on transit,
- good monitoring.
https://medium.com/@sebuzdugan/understanding-the-security-implications-of-using-mcp-9bd3323ad42d
In addition, we have several security verification tools available.
Concept of using AI to evaluate MCP servers
https://github.com/JeredBlu/custom-instructions/blob/main/mcpevaluatorv3.md
An interesting way to verify publicly available MCP servers from different vendors. It is interesting that we can also use this method to verify the security of other libraries or tools
https://www.youtube.com/watch?v=LYUDUOevtqk
MCP server security verification tool
https://github.com/invariantlabs-ai/mcp-scan
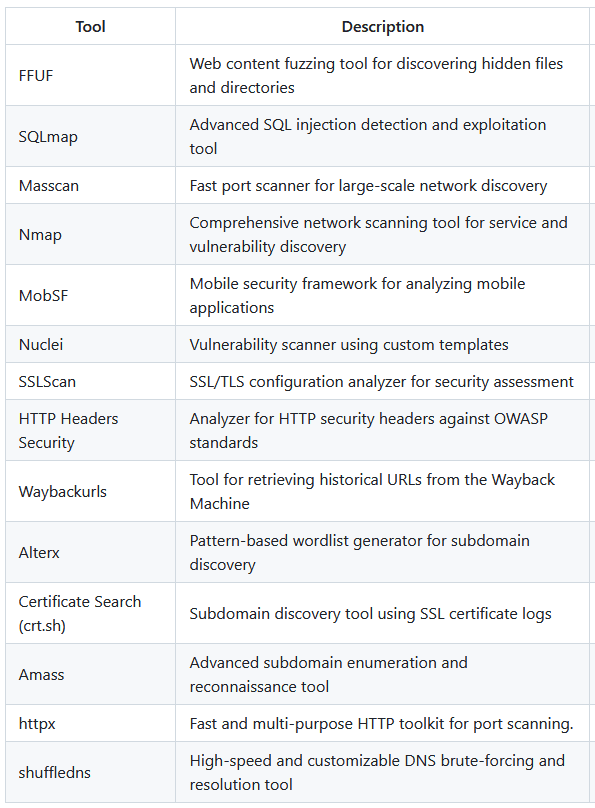
On the other hand, MCPs can also help us in daily application security.
Final thoughts
The big problem with MCP servers is the implementation itself. Especially when it is so easy to create such a server. Even more so in the vibe coding model.
The protocol itself does not define any security, which can provoke a poor implementation. However, with the right Zero Trust approach from both sides. As a Client, we don’t know what MCP will return and whether it’s secure, and as an MCP Server, we also have to be distrustful of the input.