Articles
World of secure AI
-
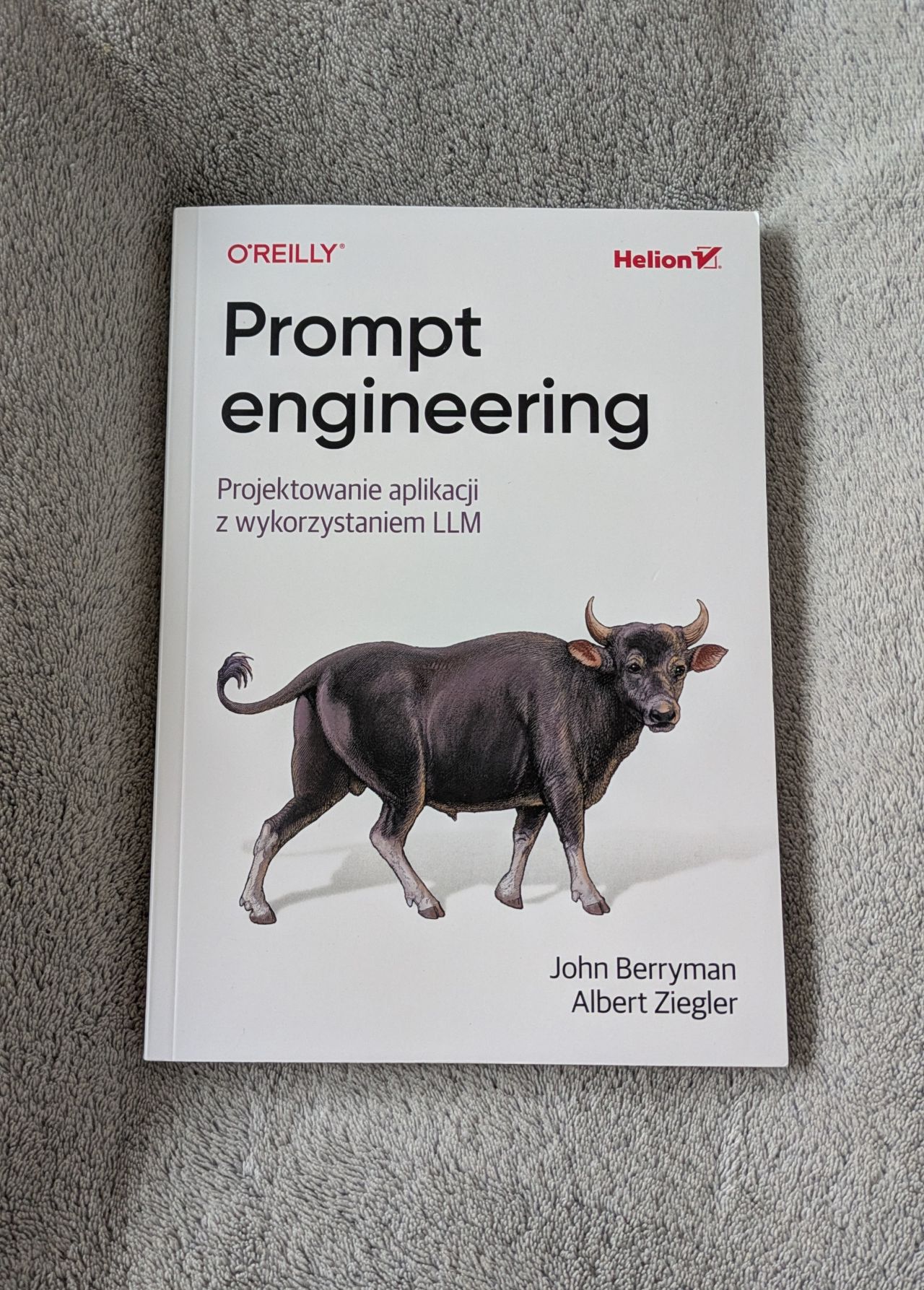
Prompt Engineering for LLMs
“Prompt Engineering” is a book that clearly communicates its target audience from the very beginning. And that’s a good thing, because this is not a book for a casual chat user who simply wants to “talk better with AI.” It is primarily aimed at developers and prompt engineers who actually build on top of models
-

AI Engineering. Building Applications with Foundation Models
“AI Engineering” is a book that combines technical precision with a practical approach to implementing artificial intelligence in organizations. The author doesn’t just describe processes—she defines them. This is not another book about AI trends, but a guide to the real mechanisms that turn a concept into a working system. Particular recognition is due to
-

Adversarial AI Attacks, Mitigations, and Defense Strategies – book review
The book Adversarial AI Attacks is unusual. On the one hand, it can genuinely put you off while reading it, and yet I kept wanting to come back to it. It’s not Stockholm syndrome, but rather the real value it carries. But let’s get to the point. At the beginning, we are met with an
-

AI Security Learning
This is the list of resources recommended by me to learn about the AI and AI Security. This is a long living list, that will evolve in time. AI future AI simple intruduction Technical perspective Mathematical perspective AI Security
-

The Developer’s Playbook for Large Language Model Security – review
This book fits perfectly into the field of AI Security, which I work with on a daily basis. That’s why I had my eye on it for quite some time. I had heard mostly positive opinions about it. In my view, there still aren’t many titles on the market that cover this topic in a
-

AI Coding Assistants security
AI coding assistants security may seem like a simple topic, but it holds a surprising number of surprises and threats.
-

MCP Security (Model Context Protocol) – short summary
MCP security is an increasingly important topic. The standard was created relatively recently, but is already implemented in many systems.